Hot Chips 31 Live Blogs: Intel/Tsinghua Xeon Jintide Security CPU
by Dr. Ian Cutress on August 20, 2019 7:40 PM EST
07:47PM EDT - Doing custom x86 CPUs is nothing new: presenting one at Hot Chips is new. Here we have Tsinghua University giving a presentation on Jintide, its custom solution built upon Intel Xeon technology.
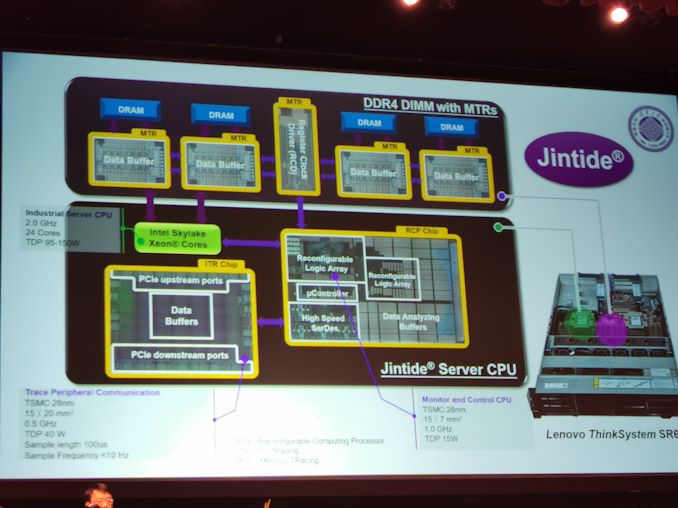
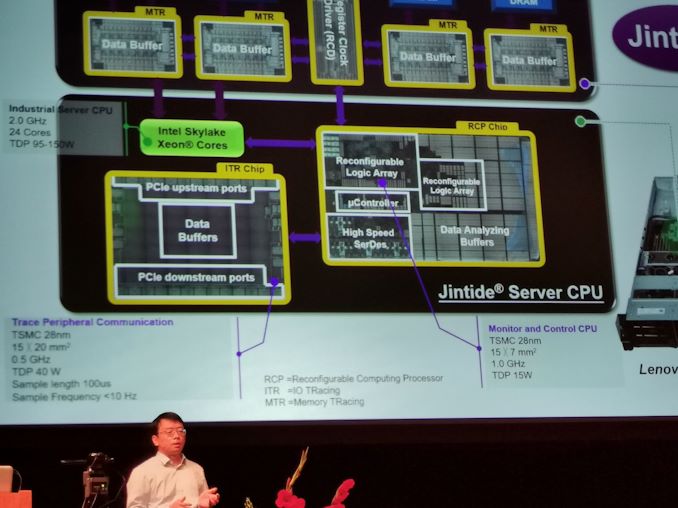
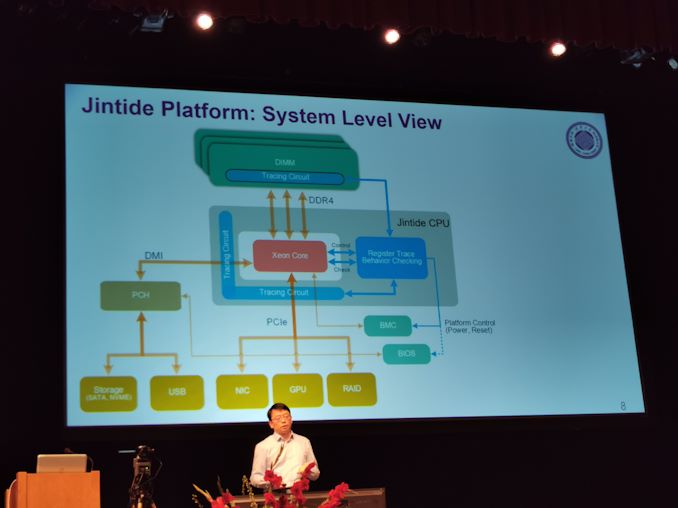
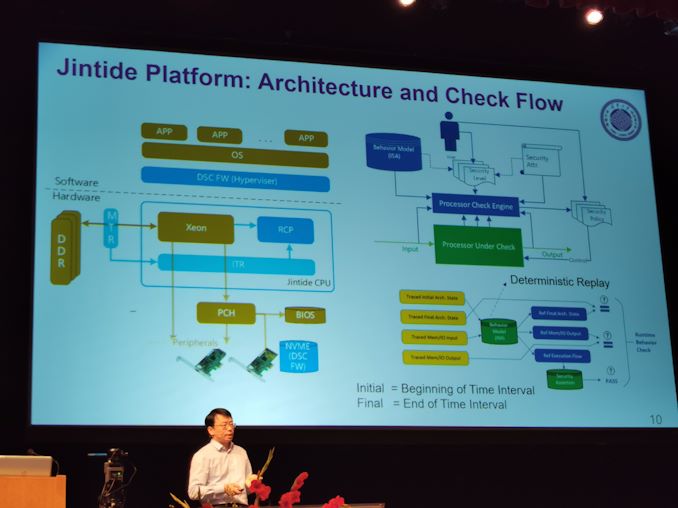
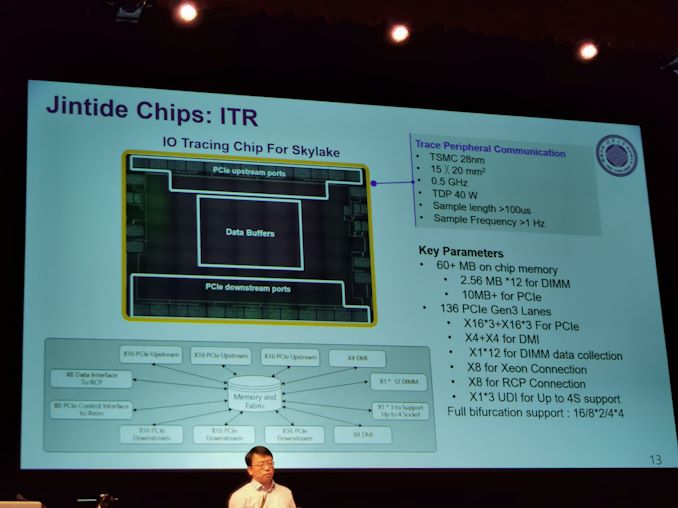
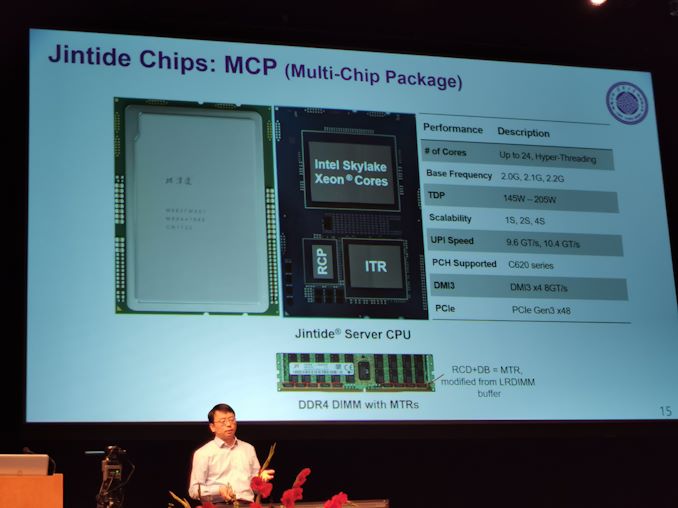
07:49PM EDT - Memory replaced with buffer tracing chip, and two added chips in the package
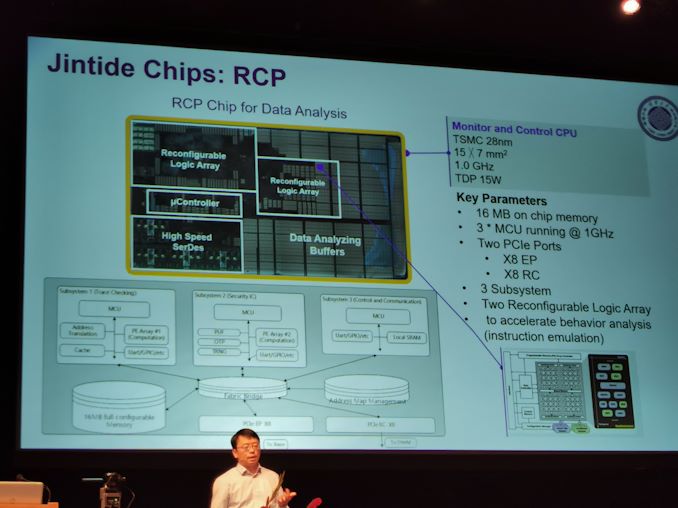
07:49PM EDT - ITR and RCP chip
07:50PM EDT - After Spectre and Meltdown, security is important
07:50PM EDT - Cheap chips have accurate layouts. Complex chips like CPUsdo not
07:50PM EDT - We do not know what is in a CPU
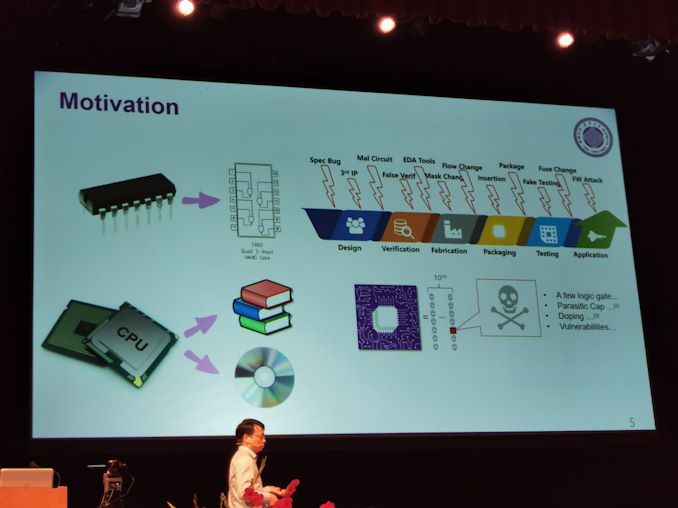
07:51PM EDT - IC industry is quite complex
07:51PM EDT - Lots of different potential attack vectors
07:51PM EDT - A modern CPU has so many transistors that a small change can add in potential vulnderabilityies
07:52PM EDT - Impossible to prove if a chip is secure/trustworthy
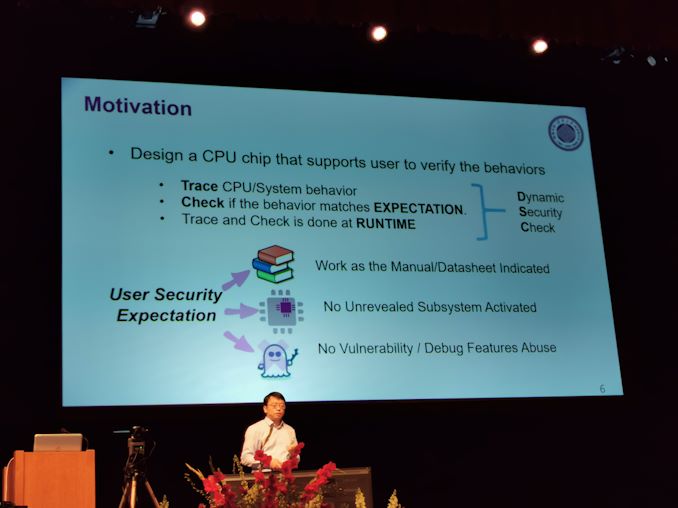
07:52PM EDT - Hardware Trust Concern: Runtime Surveillance
07:52PM EDT - Need to make sure malicious behavior is not triggered
07:52PM EDT - Need to enable a way to let the user confirm the security of the chip
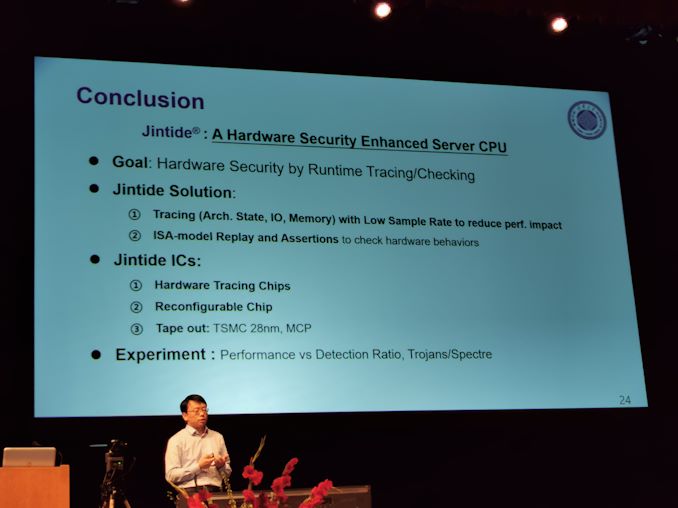
07:53PM EDT - Trace CPU/system behavior at runtime, check if the behavior matches expectation
07:53PM EDT - This is how the Jintide platform was designed
07:53PM EDT - Jintide adds in tracing capabilities for CPU validation
07:54PM EDT - Add in two TSMC 28nm chips to Intel Xeon, add it in package
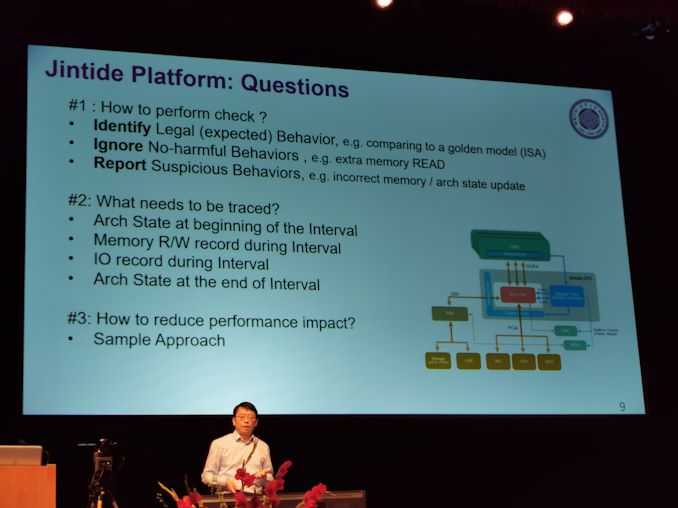
07:54PM EDT - Need to be able to perform the check, need to trace, need to avoid perforamnce impact
07:55PM EDT - Identify legal behavior, ignore non-harmful behavior, report suspicious behavior
07:55PM EDT - Works on intervals with no additional overhead
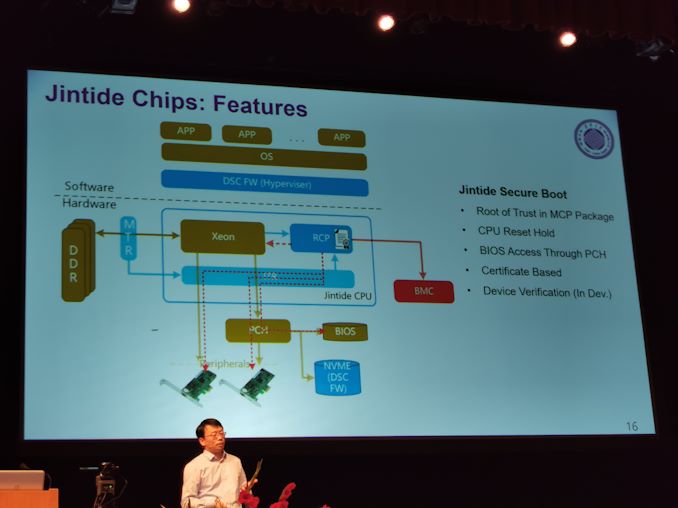
07:56PM EDT - Architecture with deterministic replay
07:56PM EDT - Runs through hypervisor
07:56PM EDT - Processor check engine
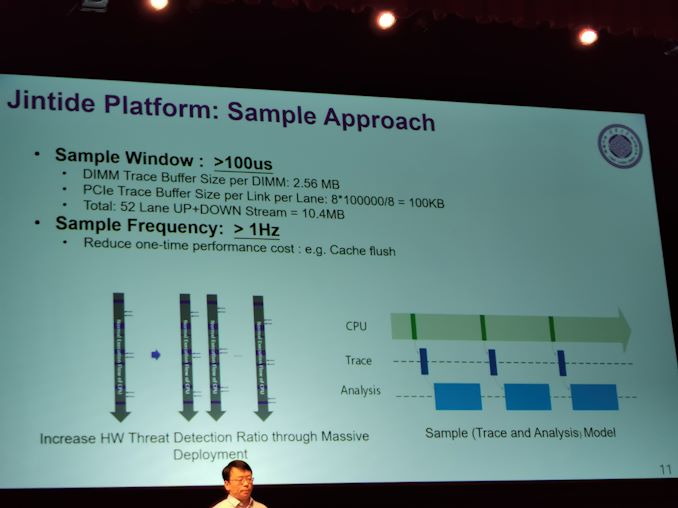
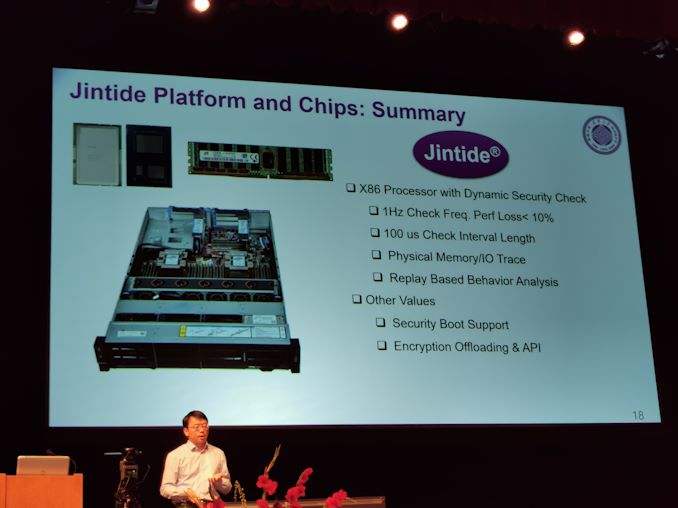
07:57PM EDT - Sample window is 100 microseconds, sample frequency is bigger than 1 Hz
07:57PM EDT - Require 10.4 MB buffer on Skylake
08:00PM EDT - RCP (re-configurable processor) and ITR chips
08:01PM EDT - Pinout is almost normal Skylake, but higher TDP
08:01PM EDT - Supports Secure Boot
08:01PM EDT - BIOS access through PCH
08:01PM EDT - Device Verification
08:01PM EDT - Certificate Based
08:01PM EDT - Up to 24 cores
08:02PM EDT - Up to 4S (so Xeon Gold?)
08:02PM EDT - PCIe 3.0 x48
08:02PM EDT - C620 PCH
08:02PM EDT - 145W-205W
08:02PM EDT - Performance loss is under 10%
08:02PM EDT - Physical memory/IO trace
08:02PM EDT - Everything traced at the physical layer
08:03PM EDT - There's a balance between detection probability and performance hit
08:03PM EDT - depends on frequency of polling
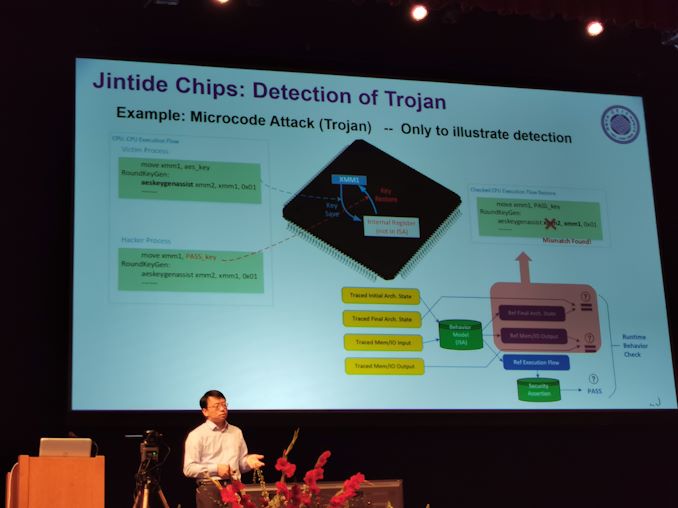
08:05PM EDT - If the microcode is attacked, can detect
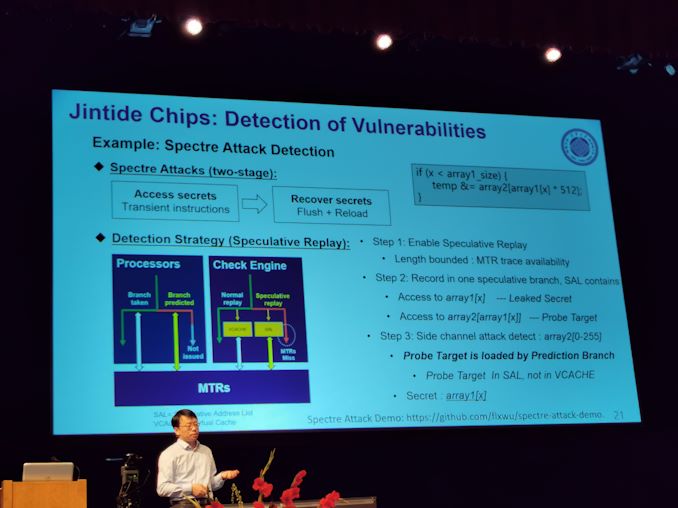
08:06PM EDT - Use the platform to detect CPU vulnerabilities
08:07PM EDT - Cannot detect by microarchitecture failures, so need to extend replay to microarchitecture level
08:07PM EDT - Spectre attack demo on Github
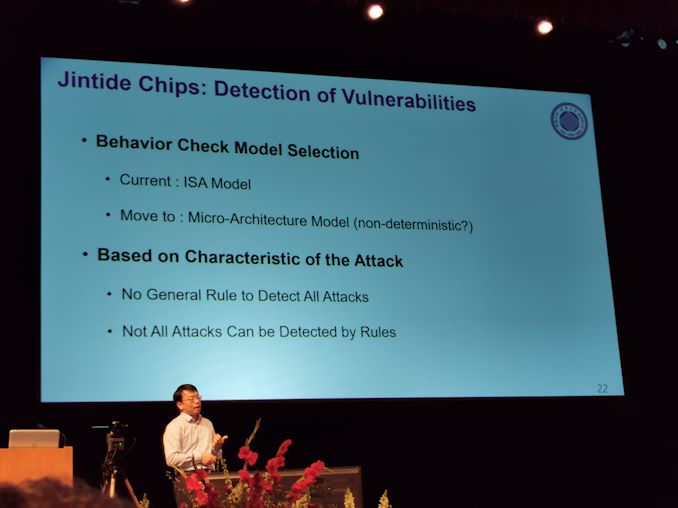
08:09PM EDT - Attack rules are based on the characteristic of the attack
08:09PM EDT - Cannot use one general rule to detect all attacks
08:10PM EDT - Trade all the physical behavior of the CPU with ISA model
08:10PM EDT - Lots of Intel involvement
08:10PM EDT - Q&A time
08:11PM EDT - Q: How are the Jintide chips attached to Xeon? A: PCIe
08:12PM EDT - Q: How can we be sure the Jintide chips don't have vulnerabilities? A: Redundancy, reconfigurable
08:12PM EDT - Q: Your chips can create attacks on the server? A: Lots of encryption features on chip, all the data on the chip is secure.
08:14PM EDT - Q: Are your chips limited to Xeon or can it do AMD, Power, or Arm? A: Xeon only.
08:15PM EDT - That's a wrap. I'm taking an hour break until the Microsoft event. There is NVIDIA/AMD GPU talks, but it's nothing we haven't seen before.










10 Comments
View All Comments
yeeeeman - Wednesday, August 21, 2019 - link
Lol, great way to secure a vulnerable chip with another ... vulnerable chip.Gondalf - Wednesday, August 21, 2019 - link
Very intersting solution in a world of unsecure cores (with no exception). Too bad AMD vulnerable core has not a solution like this in development.A good manner to retain market share in mission critical servers.
Tom Yum - Wednesday, August 21, 2019 - link
Yes, a security solution developed by a Chinese university, definitely not going to be back-doored in any way.FreckledTrout - Wednesday, August 21, 2019 - link
I assume you are trolling.eva02langley - Wednesday, August 21, 2019 - link
Intel/Xeon/China/Security...Do I need to comment to really point out the nonsense?!!!!
Phynaz - Wednesday, August 21, 2019 - link
Did you point out the nonsense when AMD sold cpu tech to the Chinese?alfalfacat - Wednesday, August 21, 2019 - link
Obviously, you have to trust the implementation of the security chip you are using. This is why Google and Apple have both designed their own security chips.The market for these is the Chinese government/military, who obviously trust themselves. There's good reason other people would not trust this particular implementation, but if you are paranoid enough to distrust your processor, you are paranoid enough to in-house your own implementation.
quadibloc - Thursday, August 22, 2019 - link
I am confused. I thought that the export of Xeon chips to mainland China was no longer permitted. So how would a university in China be involved with the design of those chips?Hindi tracks - Thursday, August 6, 2020 - link
Ab bhai jo bhi ho snapdragon ka koi tod nahi hai . I realy like to <a href="https://www.hindiamazing.com/2020/05/apple-in-hind... in hindi</a>Hindi tracks - Thursday, August 6, 2020 - link
This kind of articles are really amzing https://www.hindiamazing.com/2020/05/apple-in-hind...